China is the most active and persistent cyberthreat to American critical infrastructure, but that threat has changed over the last two decades, the Cybersecurity and Infrastructure Security Agency (CISA) says.
“I do not think it is possible to design a foolproof system, but I do not think that should be the goal. The goal should be to make it very difficult to get in,” Cris Thomas, sometimes known as Space Rogue, a member of L0pht Heavy Industries, said during testimony before the Governmental Affairs Committee May 19, 1998.
L0pht Heavy Industries was part of one of the first congressional hearings on cybersecurity threats. Members of the group warned it was possible to take down the internet in 30 minutes and that it was nearly impossible to make a defense system that was 100% foolproof. It also had difficulties when it came to tracking where threats came from.
FBI, CISA SAY CHINESE HACKERS BREACHED MULTIPLE US TELECOM PROVIDERS IN TARGETED ATTACK
“Backtracking and reverse hacking is a relatively tricky area. Based upon the relatively antiquated protocols that you are dealing with, there is not a tremendous amount of information as to where things came from, just that they came,” said another member of the group, Peiter Zatko, who testified under his codename, “Mudge.”
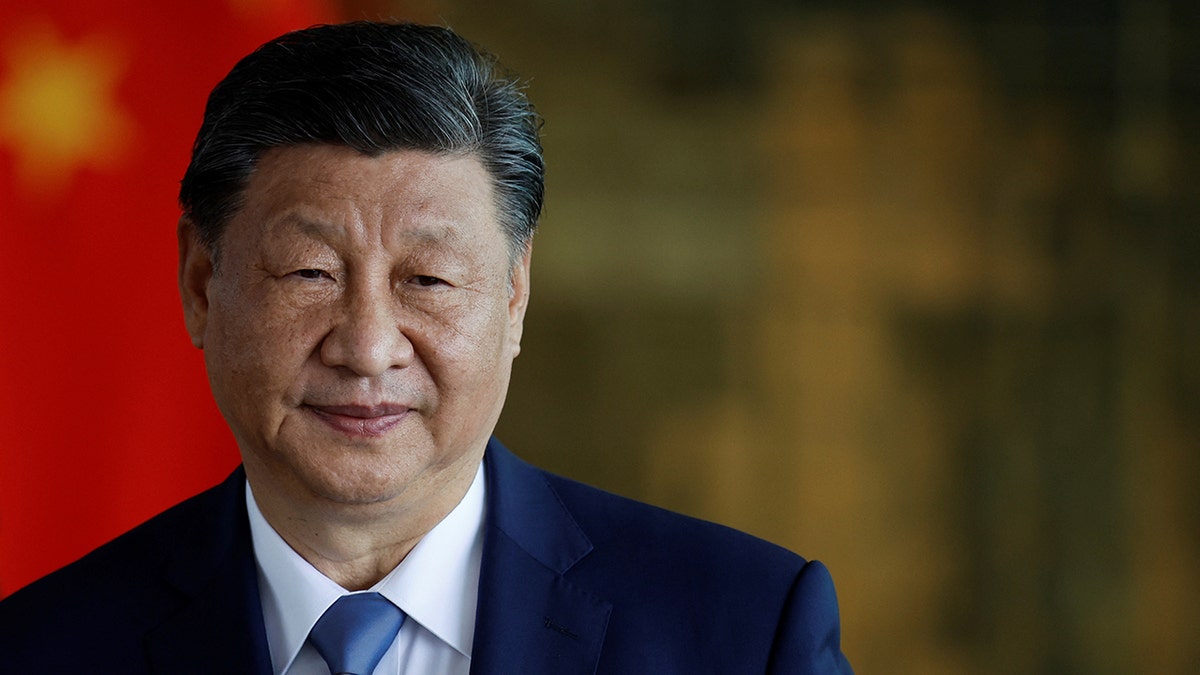
China’s President Xi Jinping attends a meeting with Brazil’s President Luiz Inacio Lula da Silva, in Brasilia, Brazil, Nov. 20, 2024. (Reuters/Adriano Machado)
By the time the hearing took place, China was likely already at work. In the early 2000s, the U.S. government became aware of Chinese espionage targeting government entities. One string of operations known as Titan Rain started as early as 2003 and included hacks on the U.S. departments of State, Homeland Security and Energy. The public became aware of the attacks several years later.
Around that time, the current CISA Director, Jen Easterly, was deployed to Iraq to investigate how terrorists were using new technology.
“I actually started in the world of counterterrorism, and I was deployed to Iraq and saw how terrorists were using communications technologies for recruitment and radicalization and operationalizing improvised explosive devices,” Easterly said.

CISA Director Jen Easterly (The Associated Press)
T-MOBILE HACKED BY CHINESE CYBER ESPIONAGE IN MAJOR ATTACK ON US TELECOMS
At that time the U.S. government was investing in cyberwarfare. The Bush administration had ordered studies on computer network attacks, but officials eventually expressed concern over the amount of damage those attacks could cause. Instead, the U.S. moved to a more defensive posture that focused on defending against attacks.
“When I stood at the Army’s first cyber Battalion and was involved in the stand-up of U.S. Cyber Command, we were very focused on nation-state adversaries,” Easterly said. “Back then, China was really an espionage threat that we were focused on.”
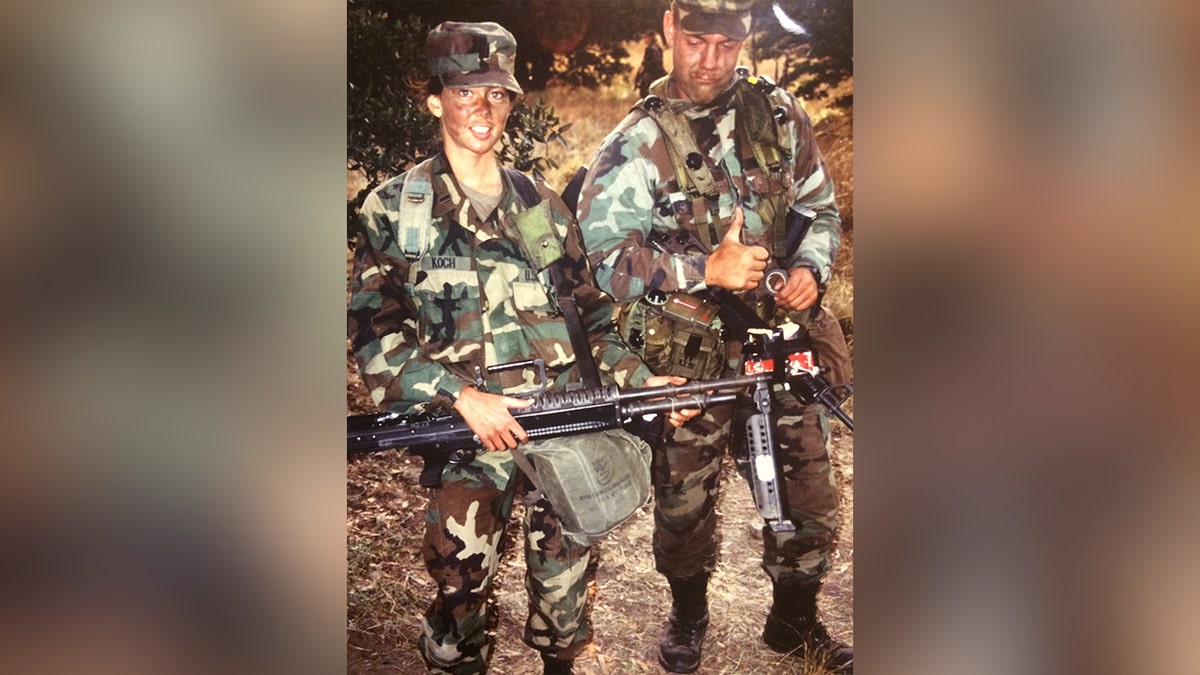
Jen Easterly, left, was previously deployed to Iraq to study how terrorists used new communications technology for recruitment. (Jen Easterly)
Threats from China would eventually intensify. According to the Council on Foreign Relations’ cyber operations tracker, in the early 2000s, China’s cyber campaigns mostly focused on spying on government agencies.
“Officials have rated China’s aggressive and wide-ranging espionage as the leading threat to U.S. technology,” Sen. Kit Bond, R-Mo., warned in 2007.
By then, China had a history of spying on U.S. innovation and using it to replicate its own infrastructure. In 2009, Chinese hackers were suspected of stealing information from Lockheed Martin’s Joint Strike Fighter Program. Over the years, China has debuted fighter jets that look and operate like U.S. planes.
CHINESE HACKERS OUTNUMBER FBI CYBER PERSONNEL ‘BY AT LEAST 50 TO 1,’ WRAY TESTIFIES
“China is the preeminent threat to the U.S.,” Easterly said. “We are laser-focused on doing everything we can to identify Chinese activity, to eradicate it and to make sure we can defend our critical infrastructure from Chinese cyber actors.”
In 2010, China shifted its targets to the public sector and began targeting telecommunications companies. Operation Aurora was a series of cyberattacks in which actors conducted phishing campaigns and compromised the networks of companies like Yahoo, Morgan Stanley, Google and dozens more. Google left China after the hacks and has yet to return its operations to the country. By the turn of a new decade, evidence showed China was also spying on critical infrastructure in the U.S. and abroad.

Easterly said the U.S. is focused on doing everything possible to identify Chinese espionage. (CISA)
“Now we are looking at them as a threat to do disruptive and destructive operations here in the U.S. That is really an evolution that, frankly, I was not tracking and was pretty surprised when we saw this campaign,” Easterly said.
The Council on Foreign Relations Cyber Operation Tracker reveals China has frequently targeted trade operations and military operations in the South China Sea, and one of its favorite targets in the past decade has been Taiwan.
CLICK HERE TO THE FOX NEWS APP
“We have seen these actors burrowing deep into our critical infrastructure,” Easterly said. “It’s not for espionage, it’s not for data theft. It’s specifically so that they can launch disruptive or destructive attacks in the event of a crisis in the Taiwan Strait.”
Taiwan is the world’s largest producer of semiconductors, and data shows how China has spied on all companies involved in all parts of that supply chain from mining to semiconductor producers.
“A war in Asia could have very real impacts on the lives of Americans. You could see pipelines blowing up, trains getting derailed, water getting polluted. It really is part of China’s plan to ensure they can incite societal panic and deter our ability to marshal military might and citizen will. This is the most serious threat that I have seen in my career,” Easterly said.
China’s public and private sector are closely intertwined by regulation, unlike in the U.S., where partnerships are key for defense.
“At the end of the day, it is a team sport. We work very closely with our intelligence community and our military partners at U.S. Cyber Command. And we have to work together to ensure that we are leveraging the full tools across the U.S. government and, of course, working with our private sector partners,” Easterly said.
“They own the vast majority of our critical infrastructure. They are on the front lines of it. And, so, ensuring that we have very robust operational collaboration with the private sector is critical to our success in ensuring the safety and security of cyberspace.”